Services delivered with long term risk mitigation goal in mind, will produce recommendations and reports about systems that need to be introduced, controls implemented, or findings resolved.
Increasing regulatory compliance within the public and private sectors requires strong service and security policies, processes, and controls that force organizations to adopt ICT based standards and frameworks for a long-term approach to mitigate the risk.
Implementation of Information Security Management System (ISMS) is a systematic and sustainable approach on how to design information security processes and appropriately delegate the accountabilities and responsibilities to a risk/process owners. Very often this ISMS relates and includes privacy and regulatory compliance requirements as a specific aspects of implementation.
Simplify a complex world!
INTEGRA Solution is established in 2004 and since the very beginning we’ve been dedicated to manage the Digital Risk for the regulated industries.
The company stands out with its dedication to IT Service and Security services with many years of hands-on experience in a host of industries, delivering numerous IT service and security solutions to banking, telecom, government and supporting industries.
COMPANY
INTEGRA Solution provides Principle statements
Our principles in Risk Management lifecycles are comprehensive and consider people, processes and technology required to embrace digital risk exposures and manage them within the risk tolerance.
Key resilience principle goals are to support business outcomes by protecting the information flows and assure risk-based decision making, rather than solely protect the infrastructure.
Our deliverables are designed to empower key IT service and security professionals to fully accept their accountabilities, in a way that enables them to completely discharge their responsibilities.
Our Holistic view of Information systems and services defines comprehensive scope of delivery that creates internally correlated and fully compliant Management System that breeds Trust and supports organization Mission.
Principle statements
Real time adaptive Risk lifecycle
These solutions and services provide continuous visibility and adaptive risk assessment in real time as security platform for resilience.
SERVICE
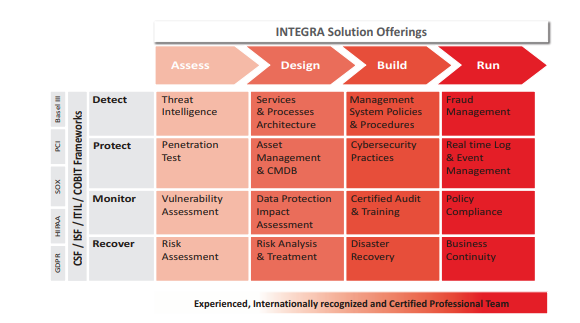
INTEGRA Solution Detect Protect Monitor Respond
All the deliverables of long time Risk lifecycle are not means to an end because they become effective only if they are operationalized in a production environment. Our unique value proposition is that we know how to transit into a production security architecture through the services and technology solutions we offer. These solutions and services provide continuous visibility and adaptive risk assessment in real time as security platform for resilience.
Whatever is implemented it could be sustainable only if it improves over time so we should always Monitor, Assess and Adjust posture, to adapt to the changes in the environment, infrastructure, threats and to establish data driven risk decision making cycle and ownership.
CAPABILITIES
Rethink your risk and security strategy.
We must admit that our security gates are open, as a way of how we are doing business and that we do not trust even our digital identities anymore. At the same time what was the security risk mitigation yearly cycle becomes, risk adaptive day to day battle and the perimeter is not a fortress anymore but it is scattered across our endpoints. The solution is how to embrace the digital risk in real time and deploy security architecture as a part of risk and trust assessment to stay resilient while delivering the services.
SOLUTIONS
INTEGRA Solution Detect Protect Monitor Respond
First we offer set of services from the security consulting capabilities and on the basis of Risk and trust assessment we decide what is the recommended security strategy and architecture that the company needs, based on the risk profile and mandates.
As an output we will recommend security architecture building blocks i.e. consultancy, services, and technology solutions with the intrinsic value to the business objectives of service delivery, balancing the costs and benefits of managing risk.
Practically this means that depending on the depth, details and specificity that company requires some of the consultancy services like GAP Analysis, Security Assessment, Risk or Data Protection Assessment will be delivered to obtain GAP Report, Security Architecture and Risk Treatment plan respectively. If the requirement of the client is about particular system, mandate or standard then the appropriate regulatory consultancy service is delivered as well as training or audit.
TRAINING & EVENTS
First we offer set of services from the security consulting capabilities and on the basis of Risk and trust assessment we decide what is the recommended security strategy and architecture that the company needs, based on the risk profile and mandates.
Resources




















Email:
contact@integrasolution.com.mk
 English
English